Cybersecurity researchers are warning about an ongoing wave of attacks targeting exposed MongoDB database instances on the internet. In these attacks, hackers are not stealing data — instead, they are completely deleting databases and replacing them with ransom notes demanding payment.
The attacks mainly affect MongoDB servers that are misconfigured and accessible without authentication. Attackers use automated scanning tools to find such databases, gain access within seconds, erase all collections, and then create a new database containing a ransom message. Victims are asked to pay a small amount in cryptocurrency in exchange for a claimed data recovery solution.
Security experts have made it clear that paying the ransom does not guarantee data recovery. In many reported cases, the deleted data could not be restored even after payment, as attackers often do not possess any real backups. The attack works more like data destruction combined with extortion, rather than traditional ransomware.
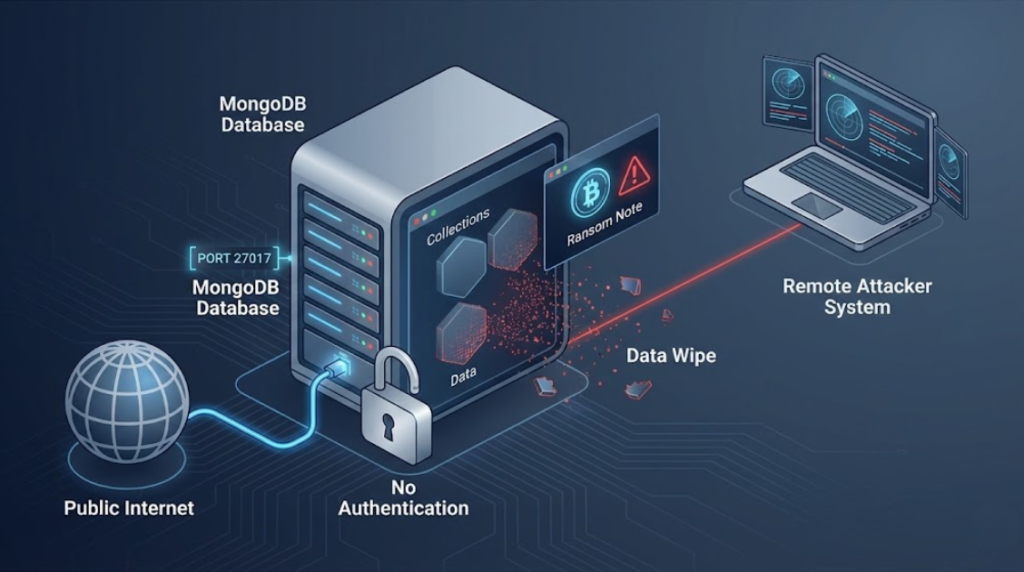
Researchers have observed that thousands of MongoDB instances remain publicly exposed, often due to default configurations, lack of firewall rules, or databases being directly accessible from the internet. These attacks do not rely on advanced vulnerabilities or zero-day exploits — they succeed mainly because of basic security misconfigurations.
Administrators are strongly advised to restrict public access to MongoDB, enable authentication, use network firewalls, and ensure regular backups are in place. Experts emphasize that properly configured MongoDB servers are not affected by this campaign.
This incident is a reminder that even simple configuration mistakes can lead to serious data loss. Organizations and developers using MongoDB must treat database exposure as a critical risk, not a minor oversight.
