Artificial intelligence is not only being used for innovation — it is also being abused by cybercriminals to steal personal data at scale. In 2026, attackers no longer rely on basic phishing emails or malware alone. Instead, they use AI to automate, personalize, and scale attacks that trick people and systems into handing over sensitive information.
This article explains how AI-powered data theft works and what individuals and businesses can do to reduce their risk.
How AI Is Used to Steal Personal Data
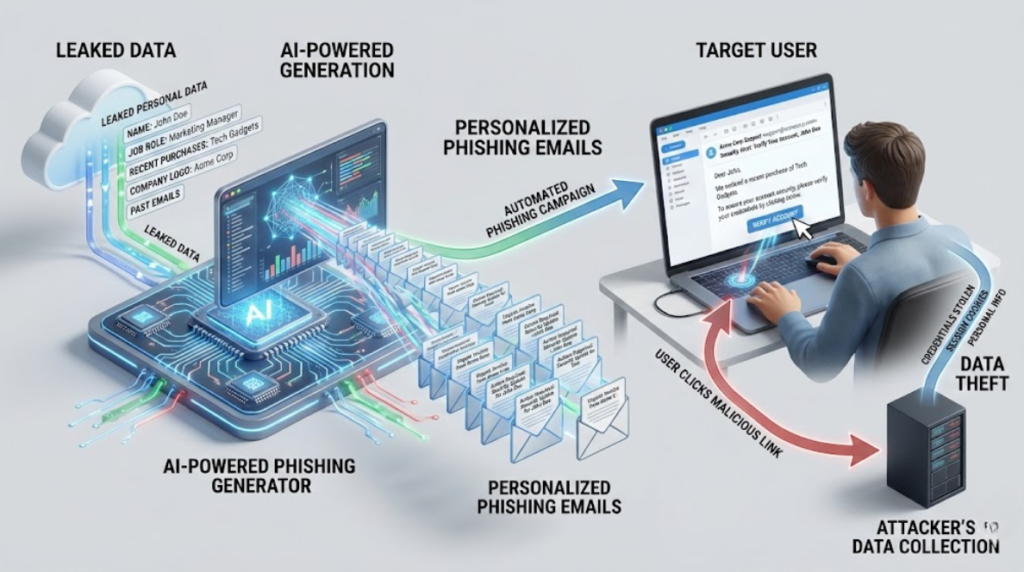
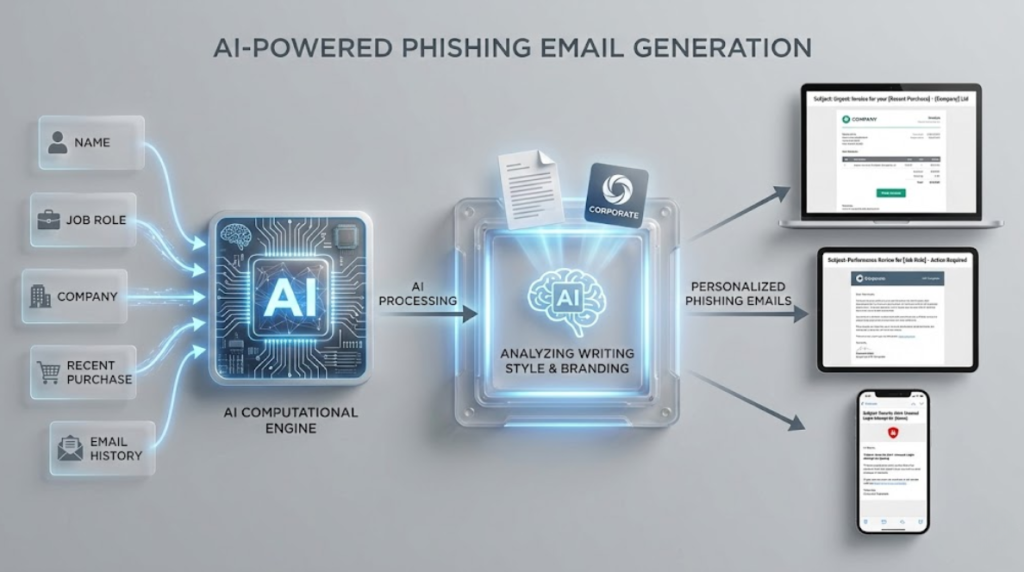
1. AI-Generated Phishing That Looks Real
Modern phishing is no longer poorly written or easy to detect.
AI tools are now used to:
- Generate perfect emails in the victim’s language and writing style
- Mimic company branding and communication tone
- Customize messages using leaked data from past breaches
Attackers can automatically create thousands of unique, personalized phishing emails that look legitimate, making detection difficult.
2. AI Voice Cloning and Impersonation

AI voice cloning can recreate a person’s voice using just a few seconds of audio from social media, videos, or calls.
Attackers use this to:
- Impersonate company executives
- Call finance or HR teams requesting urgent transfers
- Trick family members into sending money or information
These scams work because the voice sounds authentic and familiar.
3. AI-Powered Fake Websites and Portals
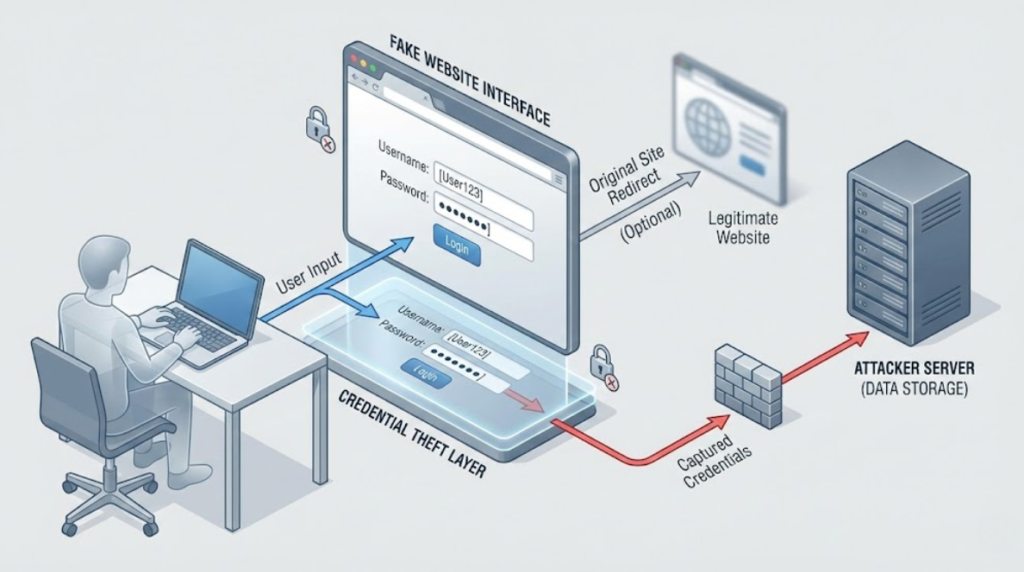
AI can instantly generate:
- Fake login pages that look exactly like Google, banks, or social platforms
- Fake customer support chats that behave like real agents
- Fake verification portals that collect identity documents
Victims believe they are interacting with a real company, but they are actually giving data to attackers.
4. AI-Driven Data Correlation
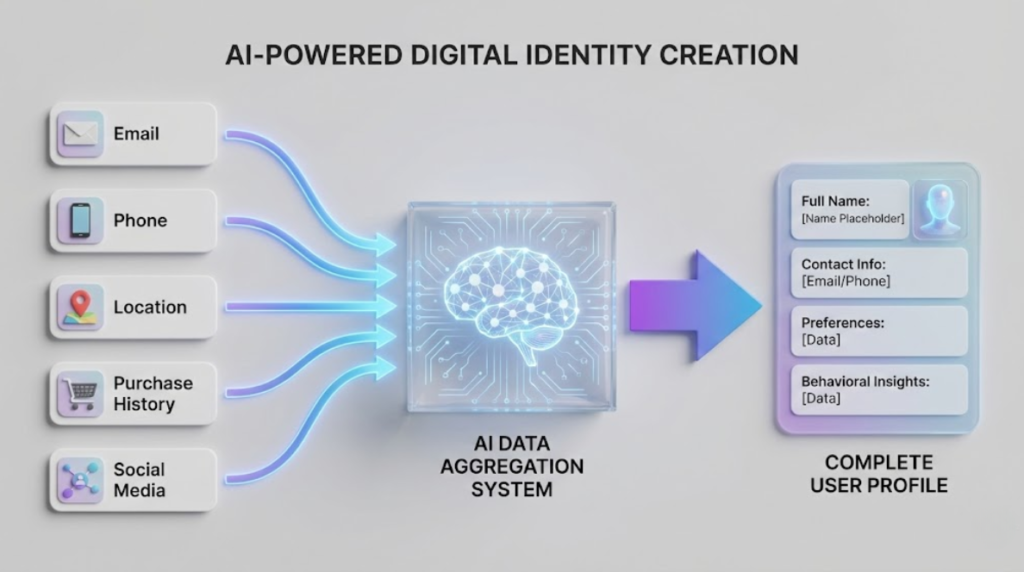
Instead of stealing all data from one source, attackers now:
- Combine small leaks from multiple breaches
- Use AI to match emails, phone numbers, names, and behavior patterns
- Build complete digital profiles of individuals
This allows identity theft, account takeovers, and financial fraud using partial data that seems harmless on its own.
5. AI-Enhanced Malware and Info-Stealers
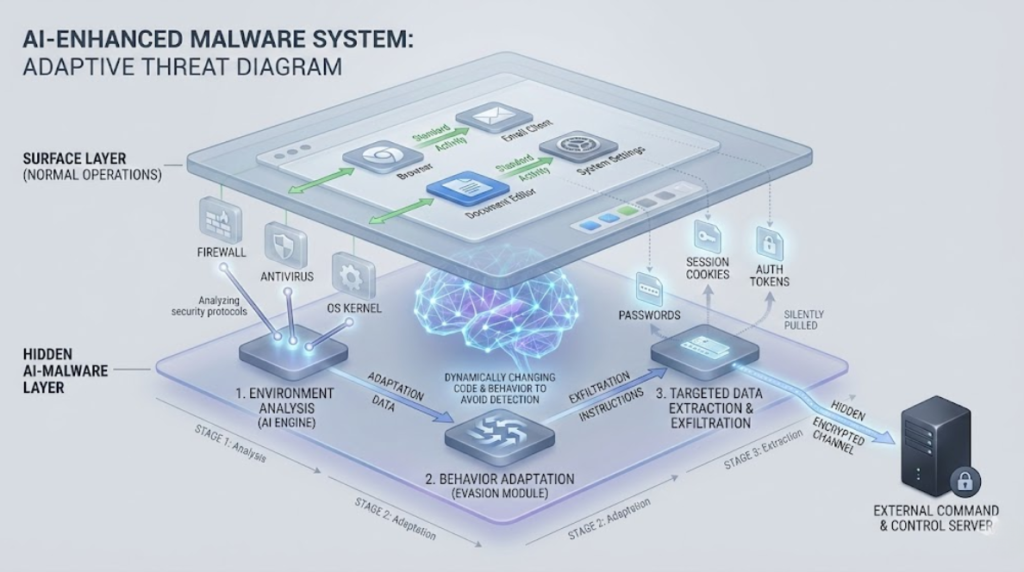
AI is also used to improve malicious software by:
- Making it adapt to different security environments
- Avoiding detection by changing behavior dynamically
- Selecting high-value data like passwords, cookies, and tokens
This increases the success rate of attacks while lowering visibility.
The Impact of AI-Driven Data Theft
- Personal identities can be misused for loans, SIM swaps, and financial fraud
- Business accounts can be compromised through credential theft
- Reputations can be damaged using impersonation and fake content
- Victims often realize the damage only after financial or legal consequences occur
How to Protect Yourself and Your Organization

1. Strengthen Identity Protection
- Use multi-factor authentication (MFA) everywhere possible
- Avoid SMS-based verification when better options exist
- Use a password manager with unique passwords per service
2. Be Skeptical of Urgent or Emotional Requests
AI scams often create urgency:
- “Immediate action required”
- “Your account will be closed”
- “Emergency transfer needed”
Always verify using a second communication channel.
3. Verify Voices and Messages
If you receive a sensitive request:
- Call back using a known number
- Confirm internally before taking action
- Never trust voice alone for financial or data-related decisions
4. Reduce Public Exposure
- Limit personal information shared publicly on social media
- Avoid posting phone numbers, birthdays, or documents
- Review privacy settings on platforms regularly
5. Monitor for Data Exposure
- Use breach monitoring tools or alerts
- Watch for suspicious account activity
- Act immediately if you see unusual logins or messages
Conclusion
AI has changed the way cybercrime operates. Attacks are no longer random, noisy, or obvious — they are personalized, automated, and psychologically convincing.
Understanding how AI is used for data theft is the first step toward reducing your risk. By strengthening authentication, verifying communications, limiting data exposure, and staying alert, individuals and organizations can significantly reduce the impact of these emerging threats.