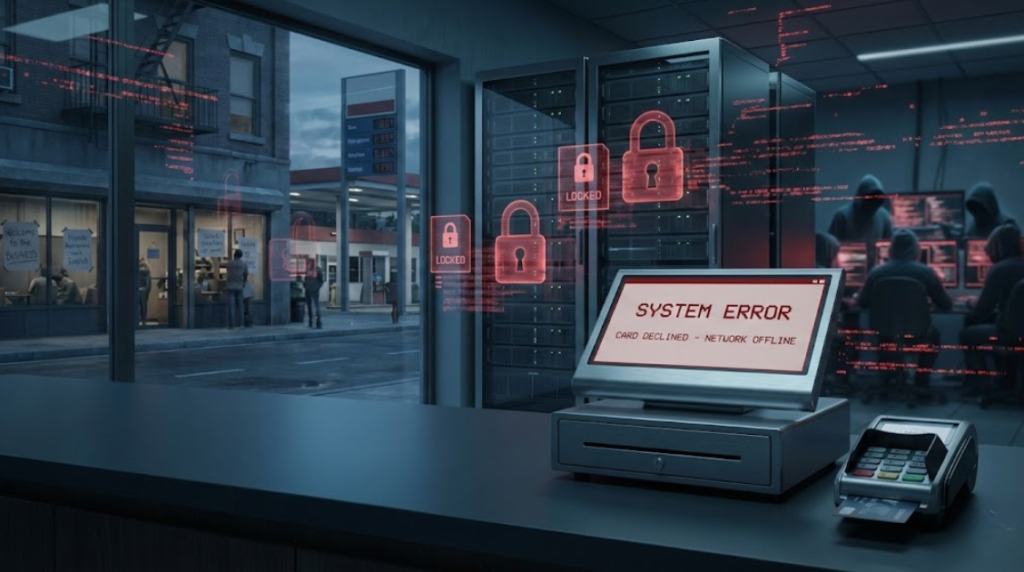
A ransomware attack has disrupted operations at BridgePay Network Solutions, a U.S.-based payment processing platform used by merchants, local governments, and service providers across the country. The incident caused a widespread outage, preventing businesses from processing card payments and accessing key transaction systems.
The disruption began when multiple BridgePay services suddenly went offline, including payment gateways, hosted checkout pages, reporting dashboards, and merchant management portals. As the outage continued, the company confirmed that the cause was a cybersecurity incident involving ransomware.
According to BridgePay, the attack resulted in system encryption, not a routine technical failure. The company stated that it immediately isolated affected systems and brought in external cybersecurity experts to assist with incident response and recovery.
Real-World Impact on Businesses and Services

The outage quickly affected day-to-day operations. Many U.S. merchants reported being unable to accept credit or debit card payments, forcing some businesses to switch temporarily to cash-only transactions. In certain areas, online billing portals connected to BridgePay services were also taken offline, delaying customer payments and administrative processes.
Businesses relying on integrated point-of-sale platforms and third-party payment tools that route transactions through BridgePay experienced service interruptions, highlighting how dependent modern commerce has become on centralized payment infrastructure.
Investigation and Data Safety Status
BridgePay confirmed that it has notified and is cooperating with federal law-enforcement authorities, including agencies responsible for cybercrime investigations. Digital forensics teams are currently analyzing the scope of the attack.
As of the latest update, the company stated that there is no confirmed evidence of payment card data theft, and that the attack appears to have focused on encrypting systems rather than exfiltrating customer information. However, the investigation is ongoing, and full conclusions will depend on forensic findings.
Service Restoration Ongoing
The company has not provided a fixed timeline for complete restoration, stating that systems will only be brought back online after thorough security validation. Status updates continue to be published as recovery efforts progress.
Security experts note that ransomware attacks on payment processors pose a particularly high risk, as even short outages can disrupt commerce, public services, and financial workflows at scale.
Why This Incident Matters
This attack is another reminder that ransomware groups increasingly target critical financial infrastructure, not just individual companies. Payment processors represent high-value targets because downtime directly impacts thousands of downstream users.
The incident also underscores the importance of:
- Network segmentation
- Incident response readiness
- Backup isolation and recovery testing
- Transparent communication during cyber incidents
As ransomware operations become more sophisticated, attacks on shared service providers are likely to continue.