1. Nessus

Type: Vulnerability Scanner
What it does:
Nessus scans servers, networks, and systems to find known security vulnerabilities, outdated software, and misconfigurations.
Used for:
Identifying weak points in IT infrastructure before attackers can exploit them.
Why it matters:
It helps organizations understand what is exposed and what needs patching.
2. Metasploit

Type: Penetration Testing Framework
What it does:
Metasploit allows security teams to safely test whether vulnerabilities can actually be exploited.
Used for:
Simulating real-world attacks to verify the impact of vulnerabilities.
Why it matters:
It shows whether a reported vulnerability is truly dangerous or just theoretical.
3. Wireshark
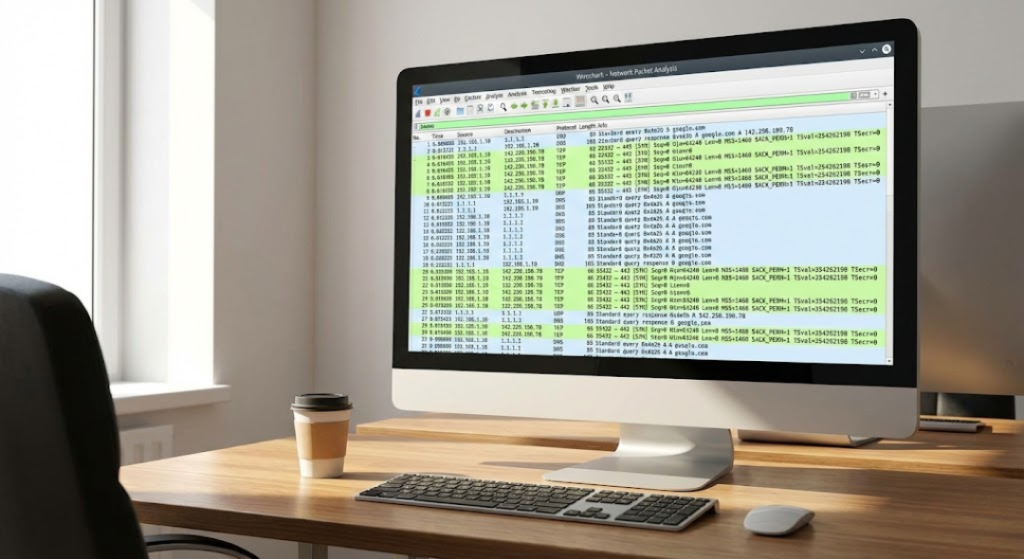
Type: Network Protocol Analyzer
What it does:
Wireshark captures and analyzes network traffic in real time.
Used for:
Investigating suspicious network activity, debugging network issues, and detecting unusual communication patterns.
Why it matters:
It helps identify data leaks, malware communication, and network misuse.
4. Splunk

Type: Log Management and SIEM Platform
What it does:
Splunk collects and analyzes logs from servers, applications, firewalls, and security tools.
Used for:
Detecting security incidents, monitoring system behavior, and investigating breaches.
Why it matters:
It provides visibility across large IT environments and helps correlate security events.
5. Burp Suite
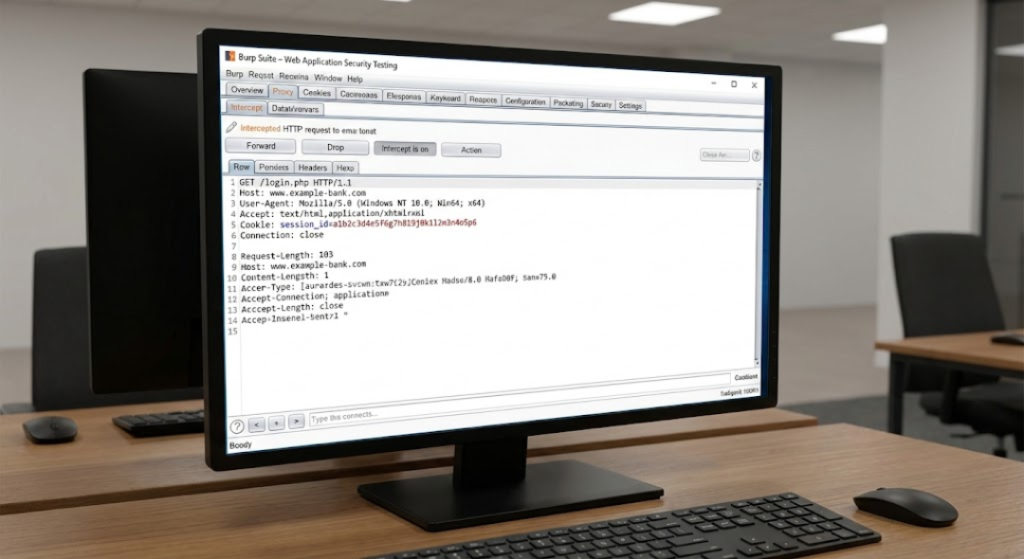
Type: Web Application Security Testing Tool
What it does:
Burp Suite tests web applications for vulnerabilities like SQL injection, XSS, authentication flaws, and logic errors.
Used for:
Finding security flaws in websites and web applications before attackers do.
Why it matters:
Most modern attacks target web apps — Burp helps secure them.
Summary
- Nessus finds vulnerabilities
- Metasploit tests exploitability
- Wireshark analyzes network traffic
- Splunk monitors and correlates events
- Burp Suite secures web applications
