A cyber espionage group tracked as Transparent Tribe has been linked to a new wave of targeted attacks against Indian government agencies, academic institutions, and strategic research organizations.
The campaign uses socially engineered delivery mechanisms and living-off-the-land binaries to deploy a remote access trojan (RAT) that enables long-term access and data collection from compromised systems.
Initial Access
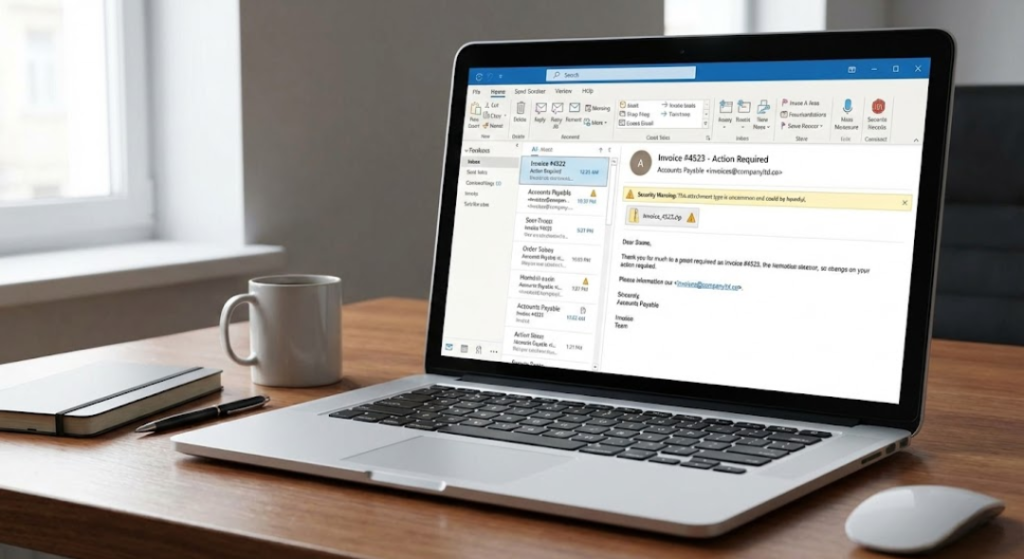
The attack chain begins with spear-phishing emails carrying compressed archives that contain Windows shortcut (LNK) files disguised as legitimate PDF documents. The LNK files are crafted to execute hidden commands while simultaneously displaying a decoy document to avoid raising suspicion.
When opened, the shortcut launches a hidden HTML Application (HTA) process via the Windows utility mshta.exe. This HTA component decrypts and loads the final payload directly into memory, minimizing disk artifacts and reducing detection by traditional antivirus tools.
Payload and Capabilities
The final stage of the attack deploys a dynamic link library that functions as a fully featured remote access trojan. The malware provides operators with capabilities including:
- Remote command execution
- File upload and download
- Screenshot capture
- Clipboard monitoring
- Process enumeration and control
- System and environment profiling
The RAT is designed to operate stealthily and maintain persistence across reboots.
Persistence Mechanisms

The malware dynamically adapts its persistence technique based on the security products present on the infected system.
If specific antivirus products are detected, the malware modifies its behavior to avoid signature-based detection. Persistence methods observed include:
- Startup folder shortcuts
- Batch script execution
- Registry-based autorun entries
- Scheduled execution via hidden scripts
This adaptive approach allows the malware to survive system restarts and maintain long-term access.
Command and Control Infrastructure
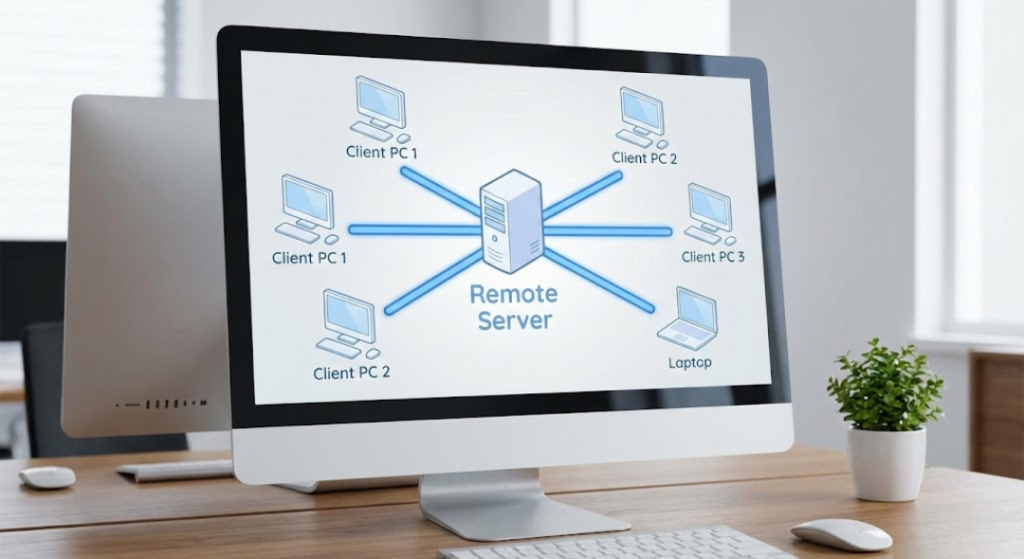
The RAT communicates with remote command-and-control infrastructure over HTTP-based channels. It periodically beacons to signal its presence and receives instructions to execute commands, retrieve additional payloads, or exfiltrate collected data.
To evade static detection, endpoint strings and configuration values are stored in obfuscated form and reconstructed dynamically during runtime.
Attribution
Transparent Tribe, also tracked as APT36, is a long-running cyber espionage group known for targeting Indian government entities, defense organizations, academic institutions, and policy research bodies.
The group has been active for over a decade and is associated with a family of custom malware including multiple generations of remote access tools and loaders.
Strategic Objective

The primary goal of this campaign appears to be intelligence collection rather than financial gain. The targeted sectors and malware capabilities suggest a focus on surveillance, document theft, and long-term monitoring of sensitive environments.
Ongoing Risk
Although some of the observed command-and-control servers are currently inactive, the malware’s persistence mechanisms ensure that compromised systems remain vulnerable to reactivation if infrastructure is restored.
This campaign highlights the continued use of socially engineered malware delivery and living-off-the-land techniques in state-aligned cyber espionage operations targeting strategic sectors.
