Recent security research has brought attention to a previously unknown access-control weakness affecting certain Cloudflare-protected environments. The issue involves a specific request handling path that, under limited conditions, could allow traffic to reach backend hosts even when strict security rules are in place.
According to technical analysis shared by independent researchers, the behavior was linked to how Cloudflare processes requests associated with automated certificate validation and related system paths. In some configurations, these requests were handled differently from standard web traffic, creating an unexpected route that bypassed normal filtering logic.
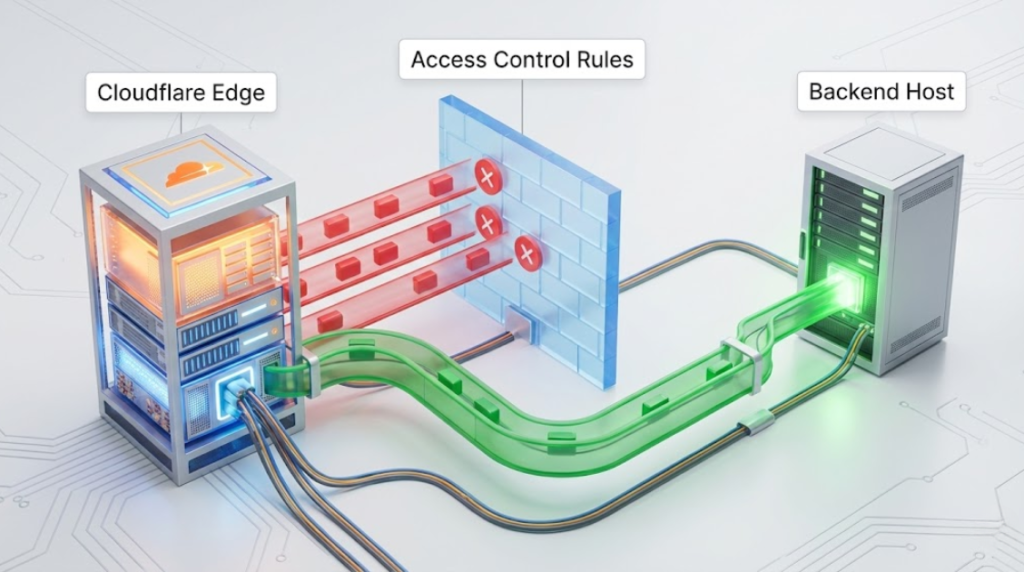
Importantly, this issue does not indicate a failure of Cloudflare’s core security architecture, nor does it suggest that all protected sites were exposed. The behavior depended on specific rule combinations and deployment scenarios. Many Cloudflare customers were not affected at all.
Cloudflare has acknowledged the report and reviewed the findings internally. The company has since implemented changes to ensure that all request paths are evaluated consistently under the same access-control and firewall policies. Cloudflare stated that the issue was addressed at the platform level and customers are not required to take action.
At this time, there has been no verified evidence of large-scale or automated exploitation linked to this behavior. The disclosure is being treated as a defensive research finding rather than an active breach scenario.
From a broader security perspective, the incident highlights a recurring challenge in modern cloud security: edge platforms must balance automation, performance, and security, and even well-designed systems can expose edge-case behaviors that require correction once identified.

Cloudflare’s response and transparency reflect standard industry practice for handling infrastructure-level security reports. Additional technical clarification may follow as part of Cloudflare’s ongoing documentation and security communications.
Why this update matters
This report is not about panic or system compromise.
It is about how security assumptions can break at unexpected boundaries, even in mature cloud platforms—and why continuous review and responsible disclosure remain essential.
