A major data breach at ADT, one of the largest home security providers in the United States, has exposed the personal information of millions of customers. The incident has now been independently verified by Have I Been Pwned, confirming the scale and authenticity of the leak.
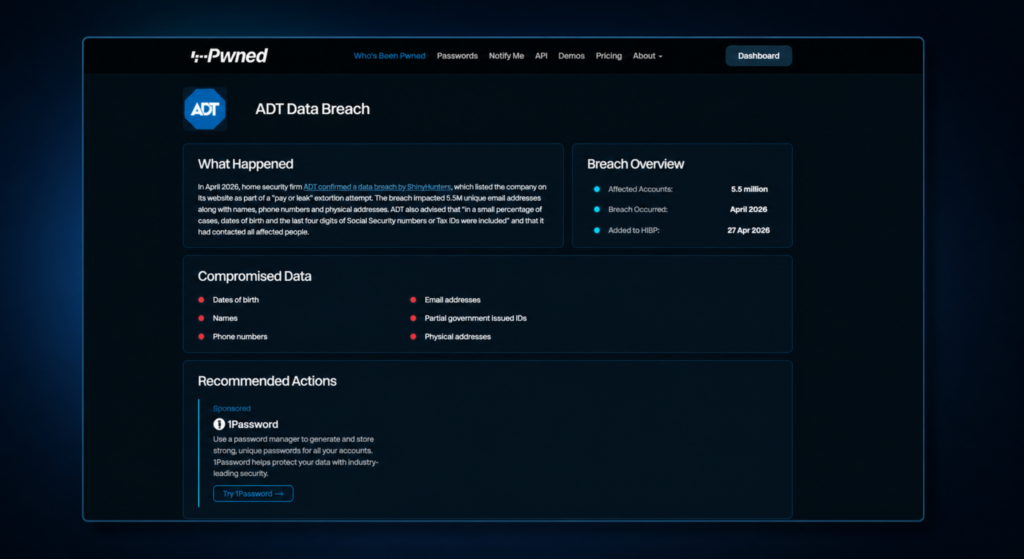
The breach, which surfaced in April 2026, affected approximately 5.5 million users. While the company has stated that its core monitoring services were not impacted, the exposure of customer data has raised serious concerns about identity-based cyberattacks and internal access security.
How the Breach Actually Happened
This was not a case of advanced malware or a zero-day exploit. Instead, the attackers relied on a far simpler method — social engineering.
According to available findings, an employee was targeted through a voice-based phishing attack, commonly known as vishing. The attacker posed as a trusted internal contact and convinced the employee to share login credentials.
Once access was gained, the attackers used the company’s single sign-on system to move into connected environments. From there, they reached a cloud-based customer database, where large volumes of personal data were stored.
This type of attack highlights a growing reality: even strong systems can be compromised if access credentials are exposed.
What Data Was Exposed
The compromised dataset includes a wide range of customer information. Based on verified disclosures, the exposed data includes:
- Email addresses (over 5.5 million records)
- Full names
- Phone numbers
- Residential addresses
In some cases, additional personal identifiers such as dates of birth and partial government-issued ID numbers were also present.
However, ADT has clarified that:
- Financial information such as credit card or bank details was not accessed
- No intrusion occurred into home security systems
- Monitoring and alarm services remain unaffected
While this reduces immediate operational risk, the exposed data is still valuable for targeted cyber fraud.
Independent Verification by Have I Been Pwned
The breach gained further attention after it was listed and verified by Have I Been Pwned, a widely trusted platform that tracks leaked data from security incidents.
The platform confirmed that millions of email addresses from the breach have been added to its database, allowing users to check whether their information was exposed.
This step is significant because it confirms that the leaked data is not just claimed, but actively circulating.
Timeline of Events
The incident followed a clear sequence:
- April 20, 2026: Unauthorized access detected and blocked
- April 23–24: ADT publicly confirms breach
- April 24: Attackers issue ransom demand
- April 27: Deadline passes without payment
- April 27–28: Data samples appear online and get verified
The attackers reportedly extracted around 11GB of data before detection, indicating that the breach remained active for a short but critical window.
The Group Behind the Attack
The breach has been linked to a known cybercrime group that specializes in data theft and extortion. Their approach is consistent across multiple incidents:
- Gain access through phishing or vishing
- Move laterally inside systems
- Extract large volumes of data
- Demand ransom under threat of public exposure
This group has been involved in several high-profile attacks in recent years, often targeting companies with large customer databases.
Why This Breach Matters More Than It Looks
At first glance, this may seem like just another data leak. But there are deeper implications.
First, it shows that attackers do not always need complex tools. A single successful social engineering attempt can bypass multiple layers of protection.
Second, it highlights the risks associated with centralized cloud systems. Once access is gained, large datasets can be extracted quickly.
Third, it raises concerns about identity-based security. Systems that rely heavily on credentials and access tokens are becoming prime targets.
What This Means for Users
For affected customers, the biggest concern is not immediate loss, but what comes next.
With access to personal details, attackers can carry out more convincing scams. Emails, calls, and messages may appear legitimate and may include accurate personal information.
Users should take the following steps:
- Check exposure status on Have I Been Pwned
- Change passwords across accounts
- Enable multi-factor authentication (MFA)
- Avoid clicking unknown links or responding to suspicious calls
- Monitor accounts for unusual activity
These steps can reduce the chances of follow-up attacks.
A Wake-Up Call for Companies
For organizations, the breach reinforces a key point — cybersecurity is not just about infrastructure, but also about human behavior.
Even with advanced systems in place, a single compromised account can lead to large-scale exposure. This makes employee awareness and training critical.
Companies need to focus on:
- Strong identity verification controls
- Monitoring unusual login behavior
- Limiting access privileges
- Regular security training
Security must be treated as a continuous process, not a one-time setup.
Conclusion
The ADT data breach is a clear example of how modern cyberattacks are evolving. Instead of breaking systems, attackers are finding ways to get inside through people.
The incident also shows how quickly exposed data can spread once a breach occurs, especially when verified by platforms like Have I Been Pwned.
For both users and organizations, the message is simple — stay alert, strengthen basic security practices, and assume that threats will continue to adapt.