Introduction: Instructure Data Breach 2026 Overview
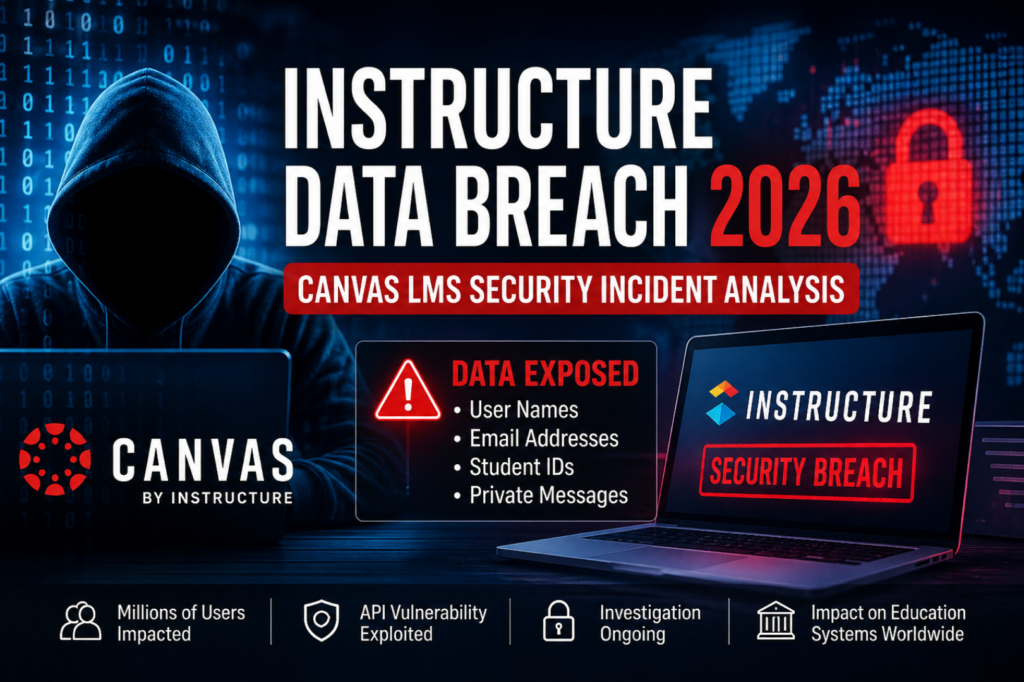
The Instructure Data Breach 2026 has emerged as a significant cybersecurity concern within the global education technology ecosystem. Instructure, the company behind the widely used Canvas LMS (Learning Management System), has been linked to a reported cybersecurity incident involving unauthorized access to certain backend systems and application-layer data.
Canvas LMS is used by universities, colleges, and online education platforms worldwide, making this incident highly impactful due to its scale and sensitivity. While investigations are still ongoing, early analysis suggests that user-related information may have been exposed through API-level weaknesses or misconfigured service endpoints.
Importantly, there is no verified indication that financial data or passwords were compromised; however, exposure of identity-related information still presents serious risks such as phishing, social engineering, and institutional disruption.
What is Instructure and Canvas LMS?
Instructure is an education technology company best known for developing Canvas LMS, a cloud-based learning management system used globally.
Canvas LMS supports:
- Online course delivery
- Student grading and assessments
- Academic communication tools
- Institutional data management
Because of its widespread adoption in higher education, any security issue affecting Canvas has the potential to impact millions of students and educators simultaneously.
Incident Summary: Instructure Data Breach 2026 Technical Analysis
The Instructure Data Breach 2026 incident is currently described as a cybersecurity event affecting backend services and API integrations. Security researchers analyzing the situation suggest that unauthorized access may have occurred through application-layer weaknesses rather than direct system infiltration.
Key Observations
- Suspicious API behavior detected
- Backend services placed under restricted access
- Investigation into potential unauthorized data queries
- External cybersecurity experts engaged
At this stage, the incident is being treated as an evolving investigation rather than a fully confirmed large-scale data breach.
Affected Systems in Canvas LMS Security Incident
The reported compromise appears to be focused on specific service components within Canvas LMS rather than full infrastructure takeover.
Potentially Impacted Systems
- API-based integrations
- Canvas Data analytics modules
- Backend user data processing systems
- Communication and messaging endpoints
This indicates a possible service-layer vulnerability, which is often exploited in modern cyberattacks targeting cloud platforms.
Data Exposure Analysis (Preliminary Findings)
Possible Data Accessed
During the Instructure Data Breach 2026, early indicators suggest that attackers may have accessed:
- Usernames and email addresses
- Student identification records
- Internal platform messages
- Limited metadata linked to academic accounts
Confirmed Not Affected (As Reported)
- Passwords (not exposed)
- Financial or billing information
- Government-issued identity documents
Although sensitive financial credentials appear safe, exposed identity data can still be used for targeted phishing campaigns.
API Data Exposure Canvas LMS: Likely Attack Scenario
Security analysts often reconstruct incidents based on behavioral indicators. In this case, the attack pattern aligns with modern API exploitation techniques.
1. Initial Access
Attackers may have gained entry through:
- Misconfigured API endpoints
- Stolen or leaked authentication tokens
- Weak access control policies
2. Privilege Escalation
Once inside, attackers may have exploited:
- Insecure session validation
- Improper token handling
- Over-permissive API roles
3. Lateral Movement
The attackers could then move across interconnected systems using trusted API relationships.
4. Data Exfiltration
Finally, data extraction may have occurred through legitimate API calls abused for unauthorized access.
This type of attack highlights the growing importance of API security in cloud-based education platforms.
Education Platform Cyberattack Risks
The Instructure Data Breach 2026 highlights broader cybersecurity risks facing digital education systems.
Key Risks Include
- Identity theft using academic email addresses
- Phishing attacks targeting students and faculty
- Disruption of online learning systems
- Loss of trust in digital education infrastructure
Because Canvas LMS integrates deeply into institutional workflows, even minor disruptions can have wide-reaching consequences.
Canvas LMS Security Incident: Indicators of Compromise (IoCs)
Organizations using Canvas LMS are advised to monitor for the following suspicious activities:
- Unusual API traffic spikes
- Login attempts from unknown geographic regions
- Token reuse or abnormal session activity
- Unauthorized access to messaging endpoints
- Increased error rates in authentication systems
Early detection is critical in preventing further exploitation.
Risk Assessment of Instructure Data Breach 2026
Severity Level: High (Preliminary)
Technical Risks
- Exposure of user identity data
- API-level abuse and system misuse
- Potential service instability
Operational Risks
- Temporary disruption in academic systems
- Delays in course management and grading
Business & Compliance Risks
- Regulatory scrutiny under data protection laws
- Institutional reputational damage
- Increased phishing targeting students and faculty
Security Recommendations for Organizations
To mitigate risks similar to the Instructure Data Breach 2026, organizations should strengthen their cybersecurity posture.
1. Strengthen API Security
- Use API gateways
- Implement strict authentication
- Apply rate limiting and schema validation
2. Improve Token Security
- Enforce short-lived tokens
- Enable automatic rotation
- Monitor session anomalies
3. Adopt Zero Trust Architecture
Every request should be verified, regardless of origin.
4. Behavioral Monitoring
Use analytics tools to detect unusual system behavior.
5. Least Privilege Access
Limit access permissions strictly based on roles.
User Safety Guidelines
Students and educators using Canvas LMS should follow these precautions:
- Enable multi-factor authentication (MFA)
- Avoid clicking unknown email links
- Monitor account activity regularly
- Report suspicious login attempts immediately
- Be cautious of phishing emails using academic branding
Strategic Cybersecurity Implications
The Instructure Data Breach 2026 reflects a growing trend: attackers are increasingly targeting education technology platforms due to their massive user bases and interconnected systems.
Key lessons include:
- API security is now a primary attack surface
- Cloud-based education systems require continuous monitoring
- Identity-based attacks are becoming more common than system-level breaches
Conclusion: Instructure Data Breach 2026 Impact Summary
The reported Instructure Data Breach 2026 highlights the evolving nature of cyber threats in the education sector. While core credentials and financial systems appear unaffected, exposure of identity-related data still represents a serious security concern.
As digital learning continues to expand globally, platforms like Canvas LMS must prioritize advanced API protection, zero-trust frameworks, and real-time threat detection to prevent similar incidents in the future.
Cybersecurity resilience is no longer optional—it is essential for protecting modern education systems