A serious security flaw has been discovered in a popular WordPress plugin called Modular DS, and attackers are already abusing it to take control of websites.
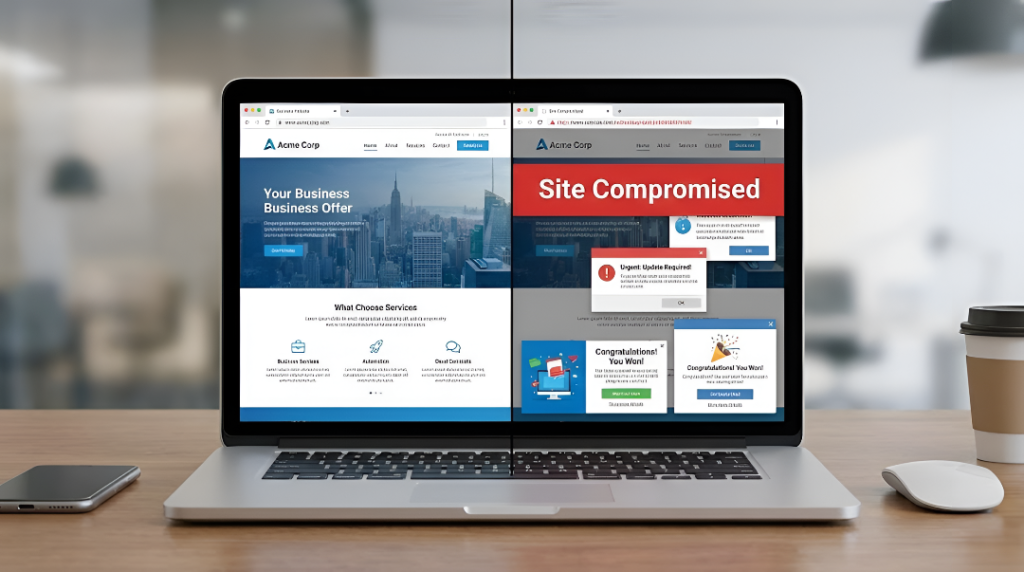
The vulnerability allows anyone on the internet to gain administrator access to a site without needing a username or password. Because of this, affected websites can be fully hijacked — content can be changed, malicious code can be inserted, users can be redirected to scam pages, and private data can be stolen.
The issue exists in all versions of Modular DS up to version 2.5.1 and has been fixed in version 2.5.2. The plugin is used on more than 40,000 websites, which makes this vulnerability especially dangerous.
What exactly is happening?

The plugin exposes a set of API endpoints used for internal communication. These endpoints were supposed to be protected behind authentication, but due to a logic flaw in how requests are verified, attackers can bypass this protection by simply adding specific parameters to their request.
Once bypassed, attackers can access sensitive internal routes — including a login route — and force the system to log them in as an administrator. This gives them full control of the website.
What attackers can do

With administrator access, an attacker can:
- Create new admin users
- Modify or delete website content
- Install malicious plugins or backdoors
- Redirect visitors to phishing or scam pages
- Steal user or system information
In many cases, victims may not notice the compromise immediately, allowing attackers to stay hidden for long periods.
Active exploitation confirmed
Security teams have confirmed that this vulnerability is not theoretical — it is actively being used in real attacks. Malicious requests targeting Modular DS sites have been detected since January 13, 2026, and several websites have already been compromised through this flaw.
What site owners should do
Anyone using Modular DS should take immediate action:
- Update the plugin to version 2.5.2 or newer
- Review admin users for anything unfamiliar
- Check server logs for suspicious API requests
- Change all administrator passwords
- Scan the site for injected or modified files
If updating is not possible right now, the safest option is to temporarily disable the plugin.
Why this matters
This incident highlights how dangerous small design mistakes can become when internal systems are exposed to the public internet without proper verification. Even a single insecure parameter can be enough to break the entire security model of an application.
Website owners should treat plugin security updates as critical, not optional — especially for plugins that manage authentication, backups, or server connections.
