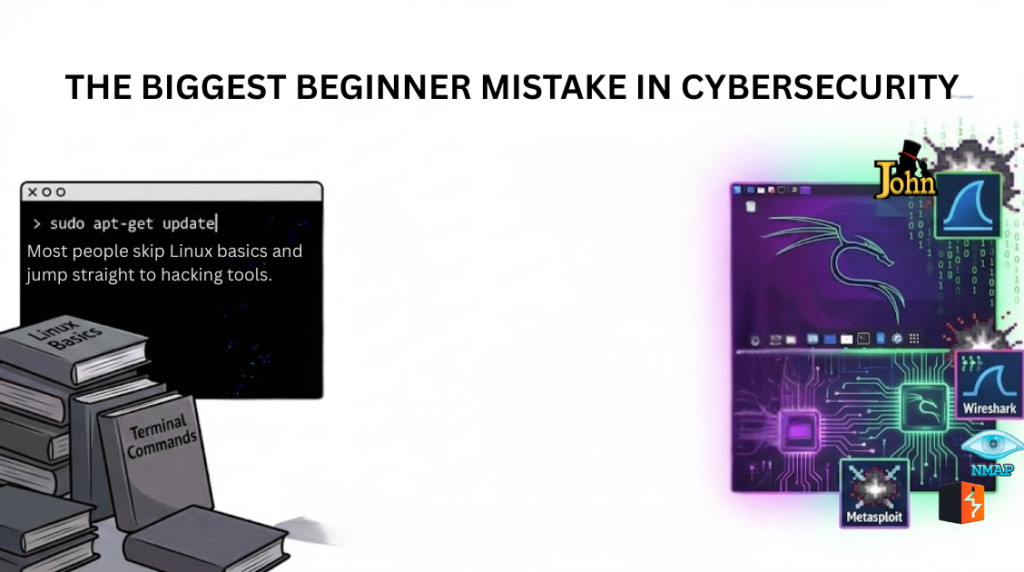
The Biggest Beginner Mistake in Cybersecurity
Today, cybersecurity is one of the most popular career choices. Social media reels, movies, and web series often show hacking as something flashy—one click, green screens, fast typing, and instant access.
Because of this, many beginners believe that real hacking means only running tools.
This is where the biggest mistake begins.
Most beginners skip Linux basics and jump directly to hacking tools. This approach creates confusion, weak skills, and false confidence.
Why Social Media & Movies Create Wrong Expectations

What you see in movies or reels is not real hacking.
In reality:
- There is no “hack in 5 seconds”
- Tools do not work magically
- Real hacking is slow, technical, and logical
- Every action depends on system behavior
Movies focus on drama.
Reels focus on views.
Cybersecurity focuses on knowledge and understanding.
What Linux Really Is
Linux is not just an operating system.
In cybersecurity, Linux is the working environment where almost everything happens.
Most servers, cloud systems, security tools, and monitoring platforms run on Linux.
If you don’t understand Linux, you don’t fully understand:
- How systems work
- How attacks happen
- How defenses are built
Why Linux Basics Are the Foundation of Cybersecurity
Linux basics teach you how a system actually behaves.
Core things Linux basics cover:
- File and directory structure
- User permissions and access control
- Processes and services
- Networking basics
- Logs and system activity
- Command-line usage
These are not optional skills.
They are the foundation.
Without them, tools become meaningless buttons.
Why Jumping Directly to Hacking Tools Is a Problem
Hacking tools are built on top of Linux concepts.
If you skip basics:
- You don’t understand tool output
- You can’t fix errors
- You don’t know what failed or why
- You blindly follow tutorials
- You depend on others instead of thinking yourself
This leads to becoming a tool user, not a cybersecurity professional.
Tools Are Not Skills
This is an important truth:
Knowing tools is not the same as knowing cybersecurity.
Tools change.
Linux concepts stay the same.
A person who understands Linux can:
- Learn any tool quickly
- Adapt to new technologies
- Analyze problems logically
- Work in real-world environments
A person who only knows tools:
- Gets stuck easily
- Panics when things break
- Cannot explain what they did
Real Cybersecurity Work Requires Linux Knowledge

In real jobs, professionals work on:
- Servers
- Logs
- Network traffic
- Security alerts
- Incident response
- Secure development environments
All of this happens in Linux-based systems.
That’s why Linux basics are required for:
- SOC analysts
- Security consultants
- Penetration testers
- Blue team engineers
- Secure developers
- Incident responders
Correct Learning Order for Beginners
To avoid confusion, beginners should follow this order:
- Linux Basics
- Networking Fundamentals
- Security Concepts
- Then Security Tools
- Practice in labs
- Real-world scenarios
Skipping step 1 breaks everything that comes after.
Why Linux Basics Make You a Better Cybersecurity Professional
Linux teaches:
- Patience
- Logical thinking
- Problem solving
- System understanding
- Real technical confidence
These are the real skills employers look for—not flashy tool demos.
Recommended Books for Beginners
If you are serious about cybersecurity, start with the right books:
- The Linux Command Line – William Shotts
Best book to learn Linux basics step by step. - How Linux Works – Brian Ward
Helps you understand how Linux systems actually work. - Cybersecurity Essentials – Charles J. Brooks
Builds strong cybersecurity fundamentals. - The Web Application Hacker’s Handbook – Dafydd Stuttard
Essential for understanding real web security, not fake hacking.
If you are learning cybersecurity:
- Don’t believe everything you see in reels or movies
- Don’t rush for shortcuts
- Don’t skip fundamentals
- Don’t confuse entertainment with reality
Linux basics are not boring.
They are powerful.
Conclusion
Linux basics are the backbone of cybersecurity.
Tools are only effective when the foundation is strong.
Those who respect the basics build real skills.
Those who skip them stay confused.
Master Linux first.
Then master cybersecurity.