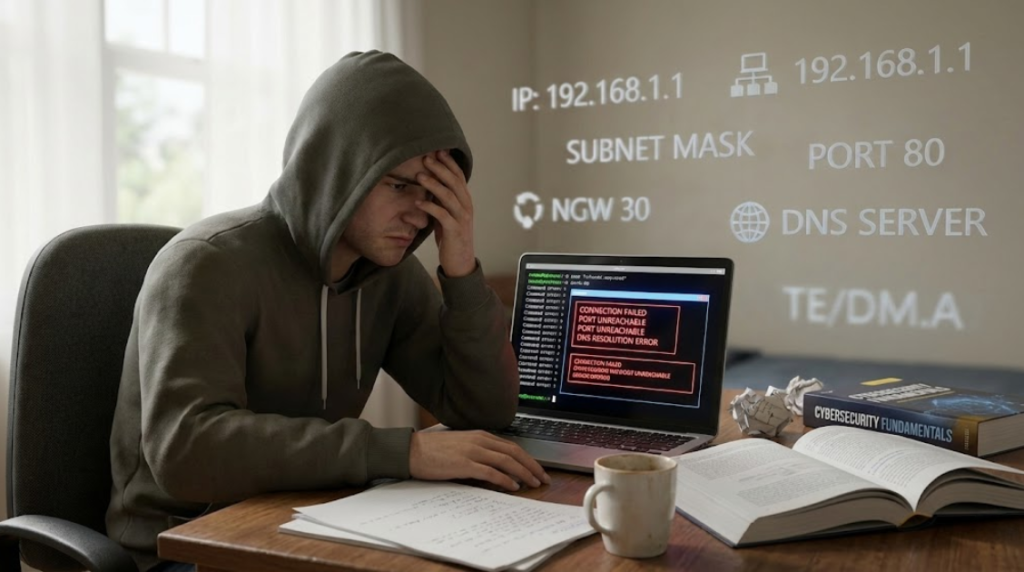
Networking is the foundation of cybersecurity. Most cyber attacks do not start with tools — they start with network communication.
Students who skip networking often feel confused later while learning SOC, VAPT, or cloud security.
This resource explains only the most important networking concepts and ports, clearly and practically.
Why Networking Is Essential in Cybersecurity
Every cyber activity depends on the network:
If you don’t understand how devices communicate, you cannot understand how attacks work.

Core Networking Concepts You Must Know
1. IP Address
An IP address is the unique identity of a device on a network.
Why it matters in cybersecurity:
- Attacker IPs are logged and traced
- Malicious IPs are blocked
- SOC teams analyze IP-based alerts
2. Ports
Ports are entry points for services.
Open or misconfigured ports increase attack risk.
Attackers always scan ports before attacking.
3. Protocols
Protocols define how data is transferred.
Important ones:
- TCP – Reliable communication (login, web, email)
- UDP – Fast but risky (often abused in DDoS)
- HTTP / HTTPS – Web traffic
- DNS – Domain resolution
4. DNS (Domain Name System)
DNS converts a website name into an IP address.
Security relevance:
- Phishing uses fake domains
- DNS hijacking redirects users
- SOC teams analyze DNS logs regularly
5. Firewall
A firewall controls what traffic is allowed or blocked.
In cybersecurity:
- Firewall logs are critical evidence
- Misconfigured firewalls cause breaches
6. LAN vs WAN
- LAN: Internal network (office, school, lab)
- WAN: Internet (external threats)
Most attacks enter from WAN and spread inside LAN.
Important Port Numbers for Cybersecurity (Only Essentials)

| Port | Service | Why It Matters |
|---|---|---|
| 22 | SSH | Remote access, brute-force target |
| 25 | SMTP | Email abuse, phishing |
| 53 | DNS | DNS spoofing & redirection |
| 80 | HTTP | Unencrypted web traffic |
| 443 | HTTPS | Secure web traffic |
| 3389 | RDP | High-risk remote desktop attacks |
🔐 Note:
You do NOT need to memorize every port.
Understanding why these ports are targeted is more important.
How Networking Is Used in Cybersecurity Roles
SOC Analyst
- Monitor network traffic
- Detect suspicious IPs and ports
- Analyze firewall and DNS logs
Ethical Hacker (VAPT)
- Scan open ports
- Identify exposed services
- Test network misconfigurations
Common Beginner Mistakes
Skipping networking basics
Jumping straight into hacking tools
Memorizing ports without understanding usage
Ignoring DNS and firewall concepts
What Is Enough for a Beginner?
You are ready to move forward if you understand:
- IP addresses
- Ports and services
- TCP vs UDP
- DNS and firewalls
This is a strong and sufficient foundation.
Final Takeaway
Networking is not optional in cybersecurity.
A weak foundation leads to confusion later.